TL;DR
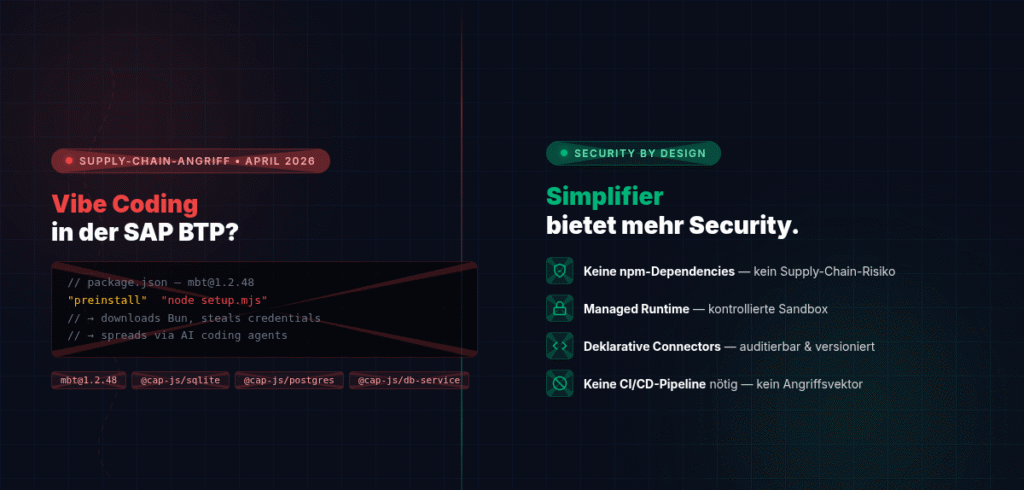
On April 29, 2026, four central npm packages of the SAP developer ecosystem were compromised – including mbt, @cap-js/sqlite, @cap-js/postgres and @cap-js/db-service. The attack stole credentials from CI/CD pipelines, cloud secrets from AWS, Azure and GCP and spread independently – including via AI coding tools such as Claude Code and VS Code. Anyone who “vibe-codes” SAP BTP, i.e. develops quickly with AI wizards and open source packages without questioning the security architecture, is exposing their company to a real risk. Simplifier offers a fundamentally different approach here.
What happened? The Shai Hulud attack on SAP packages
What sounds like science fiction is bitter reality: On April 29, 2026, StepSecurity uncovered a supply chain attack on the SAP developer ecosystem that has it all.
Four compromised packages that are part of every SAP CAP developer’s daily toolbox:
mbt@1.2.48– the SAP Cloud MTA Build Tool@cap-js/sqlite@2.2.2– the SQLite connection for SAP CAP@cap-js/postgres@2.2.2– the PostgreSQL connection for SAP CAP@cap-js/db-service@2.10.1– the central database service for SAP CAP
A simple npm install was enough to set a devastating chain in motion:
- A
preinstallhook downloaded the Bun JavaScript runtime unnoticed - An 11.6 MB obfuscated payload was executed
- npm tokens, AWS/Azure/GCP credentials, SSH keys, Kubernetes configs and even crypto wallets were stolen
- The malware spread independently to all npm packages to which the stolen token had access
The perfidious thing: The malware wrote itself into .vscode/tasks.json and .claude/settings.json – anyone who then opened the infected repository in VS Code or started a Claude Code session was infected again. The commit carried the harmless message "chore: update dependencies" and was signed with claude@users.noreply.github.com.
The first supply chain attack that uses AI coding agents as an infection vector.
What is “vibe coding” – and why is it booming in the SAP world?
The term “vibe coding” describes a development style in which developers rely heavily on AI assistants (Copilot, Claude Code, Cursor), quickly install packages, generate code and deploy with minimal review. The motto: “It works, so ship it.”
In SAP BTP, it looks like this:
-
npm installas a first step – CAP projects start with half a dozen npm dependencies - AI generates boilerplate – Claude or Copilot write service handlers, OData endpoints and DB schemas
- CI/CD pipelines run automatically – build and deploy GitHub Actions, GitLab CI or Azure DevOps
- Fast iteration – whoever delivers the fastest wins
The problem: In this flow, nobody checks what npm install is actually doing. Nobody validates preinstall hooks. Nobody monitors which network connections are established during the build.
The five security vulnerabilities of the Vibe coding model
1. uncontrolled chains of dependency
A typical SAP CAP project has npm install between 200 and 800 transitive dependencies. Each of these can contain a preinstall hook that executes any code – before the actual installation, before any audit tool, before any review.
The Shai Hulud attack exploited precisely this: A single compromised maintainer account was enough to inject the malware into the core SAP CAP packages.
2. CI/CD as a high value target
The malware recognizes 32 different CI/CD platforms – from GitHub Actions to Jenkins to Vercel. In CI environments, it reads the memory of the GitHub Actions Runner to extract all secrets – even those that were never exposed as environment variables.
Anyone who uses vibe coding and runs their SAP BTP deployments via standard CI/CD pipelines gives the malware direct access:
- SAP BTP Service Keys
- Cloud Foundry API tokens
- HANA Cloud Credentials
- Destination Service Secrets
3 AI assistants as an attack vector
The Shai Hulud attack is the first documented case of AI coding tools being misused as a persistence and propagation vector. The malware writes itself into configuration files that AI tools automatically execute at startup.
This means that anyone working with Claude Code on an infected repository automatically executes the malware with every new session – without realizing it. The AI assistant itself becomes an accomplice.
4. no runtime isolation
In classic SAP BTP development with CAP and Node.js, the entire code – including all npm dependencies – runs in the same process context. There is no sandbox, no isolation, no restriction of network access at build time.
If a preinstall hook wants to steal credentials, it can do so. If it establishes network connections to api.github.com, this will not be noticed – because this domain is permitted in every enterprise firewall.
5 Encrypted exfiltration makes forensics impossible
The attack encrypts stolen data with AES-256-GCM, where the AES key is wrapped with RSA-4096. Even if a company finds the dead-drop repositories on GitHub, it only sees ciphertext. Without the attacker’s private key, it is impossible to analyze the stolen data.
How Simplifier solves the problem at the root
Simplifier takes a fundamentally different approach to the classic “code + npm + deploy” model of SAP BTP. And it is precisely this difference that provides the decisive security advantage.
No npm dependencies, no supply chain risk
The Shai Hulud attack works because developers blindly npm install and trust that 800 transitive dependencies are secure.
This attack vector does not exist in Simplifier.
Simplifier is a low-code platform on which business logic is mapped via business objects, connectors and visual workflows – not via npm packages. The dependency on external, uncontrolled open source registries is completely eliminated. There are no preinstall hooks, no uncontrolled build scripts, no transitive dependency chains.
Managed Runtime instead of Open Runtime
In SAP BTP with CAP, your code runs in a Node.js runtime that can do everything: Network access, file system access, process spawning. This is exactly what the malware exploits.
Simplifier, on the other hand, offers a controlled execution environment:
- Business Object Functions run in a managed JavaScript sandbox
- Connectors define explicit, configured connections to external systems – no arbitrary HTTP calls at runtime
- No access to the file system or processes – the attack surface that the Shai Hulud worm exploits simply does not exist
Declarative integrations instead of code-based Wild West connections
When an SAP CAP developer needs a connection to an SAP system, he writes code. This code can do anything – including things that nobody intended.
In Simplifier, integrations are declarative:
- REST connectors with defined endpoints, login methods and SSL configuration
- RFC connectors with explicit SAP system connection
- SQL connectors with controlled database access
Each integration is configured, versioned and auditable. A compromised npm package cannot abuse an SAP RFC connection in Simplifier because there is no programmatic access to the connector infrastructure that does not run via platform governance.
No CI/CD pipeline risk
The Shai Hulud attack specifically targets CI/CD pipelines – GitHub Actions, Jenkins, Azure DevOps. This is where the most valuable secrets lie: deploy keys, cloud credentials, API tokens.
Simplifier projects do not require an external CI/CD pipeline for build and deployment. The platform manages the entire lifecycle internally:
- No build step with uncontrolled code execution
- No
npm installin a pipeline - No risk of a compromised package extracting pipeline secrets
No AI agent persistence attacks
The Shai Hulud attack writes itself in .claude/settings.json and .vscode/tasks.json files that AI coding tools execute automatically.
Simplifier development takes place on the Simplifier platform, not in local IDEs with uncontrolled extension and hook mechanisms. The attack vector “AI coding agent executes malware” does not exist in this model.
This does not mean: “Low code is always better”
Fairness requires differentiation. There are legitimate reasons to work with CAP and Node.js in SAP BTP:
- Maximum flexibility for complex, non-standardizable requirements
- Large developer community and extensive ecosystem
- Proven patterns for microservices and event-driven architectures
But with this flexibility comes responsibility. And the Shai Hulud attack shows that many companies do not bear this responsibility – because they do not know the risks, do not have the tools or do not live the processes.
The question is not “low-code vs. pro-code”. The question is: Does your security model fit your development model?
Concrete recommendations for action
If you want to stay with SAP CAP / BTP:
--ignore-scriptsSet as standard fornpm installand release hooks individually- Commit lock files (
package-lock.json) and check integrity hashes - Use StepSecurity Harden-Runner or comparable tools in CI/CD pipelines
- Activate egress monitoring in pipelines – every network connection must be explainable
- Provide npm tokens with minimal scopes and IP restrictions
- Restrict OIDC Trusted Publishing to specific branches and workflows
- Include AI-Tool configuration files (
.claude/,.vscode/tasks.json) in.gitignoreor protect them using branch protection
If you want to switch to Simplifier:
- Map existing SAP integrations as simplifier connectors (REST, RFC, SQL)
- Migrate business logic to business object functions
- Eliminate CI/CD pipeline dependencies – Simplifier manages the lifecycle
- Perform a security audit of the existing npm dependencies – you will be surprised what you find
Conclusion: The supply chain is the new battlefield
The Shai Hulud attack is not a theoretical risk. It happened on April 29, 2026. It hit SAP core packages. It stole credentials. It spread via AI coding tools. And it won’t be the last of its kind.
Vibe coding – fast, AI-supported development without security awareness – is a luxury that companies in the SAP environment can no longer afford. Not because AI tools are bad. But because the underlying model – hundreds of uncontrolled open source dependencies, open runtimes, unprotected pipelines – offers an attack surface that is actively exploited.
Simplifier offers an alternative: a platform that combines SAP integration, business logic and deployment in a controlled, managed environment – without the dependency hell, without the pipeline risks and without the attack surfaces that made the Shai Hulud worm possible in the first place.
The question is not whether the next supply chain attack is coming. The question is whether your architecture is prepared for it.
Further links:
- StepSecurity: A Mini Shai-Hulud Has Appeared – Full technical analysis of the attack
- DSAGNet Post: IMPORTANT! NPM attack!
- AI responsibility in the company